Blog
Call Bomber In: Modern Digital Communication
Published
7 months agoon
By
Callum
The phrase call bomber in modern communication typically refers to a tool or service that repeatedly sends phone calls to a single number in a short span of time. Originally developed with automation techniques and scripting, such tools have become more accessible. Their application has generated discussions in cybersecurity, ethics, and digital behavior. The core idea of using a call bomber in stems from its ability to flood a mobile or landline device with numerous calls, making it difficult for the receiver to use their phone effectively.
The advancement of telecommunication and internet technology has made such tools more powerful and widely available. A call bomber in operation can trigger hundreds or even thousands of call attempts, usually by exploiting telephony APIs or open-source frameworks. While some see these tools as humorous pranks, others recognize the serious implications, especially in terms of personal privacy, harassment, and system abuse.
Origins and Evolution of Call Bomber In Technology
To understand how the call bomber in became widespread, one must look at the evolution of automated calling systems. Initially, auto-dialers were created for businesses to handle customer service and marketing tasks. These systems could dial multiple numbers simultaneously and connect customers to human agents or pre-recorded messages.
Over time, these capabilities were repurposed by individuals looking to exploit automation for disruptive purposes. The ability to initiate thousands of call requests in minutes made the call bomber in a preferred tool for pranks, retaliation, or even competitive sabotage. With open-source libraries and VoIP (Voice over Internet Protocol) services now easily accessible. It has become relatively simple to launch a call bombing campaign with minimal technical knowledge.
While the original intent behind such systems was practical and service-oriented. The misuse of this technology has created significant problems for individuals, companies, and service providers worldwide.
You Might Also Like: Techgup org
Functionality and Technical Mechanism of a Call Bomber In
The operational logic behind a call bomber in lies in its algorithmic structure and access to communication channels. Typically, the user inputs a target phone number into an interface. The software then initiates repeated call requests using internet telephony services, either in sequential bursts or simultaneously.
Some advanced versions of call bomber in tools also allow users to schedule attacks, customize call intervals, or select from a pool of caller IDs to bypass filtering mechanisms. In more aggressive applications, the system can mask its origin through proxies and virtual numbers, making detection and prevention more challenging.
In general, these tools rely on APIs from communication platforms, including services meant for legitimate bulk calling or messaging. By reverse engineering or exploiting these services, a call bomber in application can be used for disruption, creating a situation where the target cannot receive normal calls or use their phone effectively.
Common Use Cases and Motivations
The use of a call bomber in can vary based on the intent behind it. While it is often associated with mischief, there are multiple motivations that lead to its deployment. One common scenario is prank calls, where the goal is to irritate or confuse the recipient without causing physical harm. In these cases, the tool is used briefly, and the calls often carry automated or silent messages.
Another use case is retaliation. Some users deploy call bomber in platforms to overwhelm or harass individuals they are in conflict with. This form of digital aggression can escalate quickly, creating a hostile environment for the victim. In rare but concerning cases, such tools have been used during political campaigns or business rivalries to disrupt communications and create confusion.
Activist groups have also been known to use call bombing as a form of protest, targeting hotlines or public contact numbers of organizations they oppose. While this form of digital protest is controversial, it highlights the many faces of call bomber in usage and its intersection with free expression and dissent.
Legal and Ethical Implications
One of the most significant concerns surrounding the call bomber in concept is legality. In many jurisdictions, using such tools constitutes a violation of telecommunications laws. Flooding a person’s phone with repeated calls can be classified as harassment, unauthorized access to communication systems, or even cyberstalking.
In the United States, the Telephone Consumer Protection Act (TCPA) and the Computer Fraud and Abuse Act (CFAA) have provisions that could apply to call bomber in activities. In India, sections of the Information Technology Act and the Indian Penal Code may be invoked in response to such actions. Similarly, European countries apply data protection and harassment laws to deal with cases of digital abuse involving call bombing.
From an ethical perspective, the use of call bomber in technology raises serious questions about consent, accountability, and digital rights. While some users view it as a harmless prank, others see it as a direct invasion of privacy. The line between entertainment and exploitation is often blurred, making it essential for users to understand the consequences of deploying such tools.
Impact on Victims and Emergency Services
The effects of call bomber in incidents on victims can be severe. Receiving an unmanageable volume of calls can disrupt work, sleep, and mental health. In extreme cases, victims may be forced to disconnect their phones, change numbers, or seek legal action to stop the harassment.
Moreover, the misuse of such tools can interfere with emergency services. If someone’s phone is being targeted by a call bomber in attack. They may not be able to reach out to hospitals, law enforcement, or other critical services during a real emergency. This makes the practice not just annoying, but potentially life-threatening.
Businesses are also vulnerable. Customer support lines, helplines, or booking numbers can be rendered non-functional if targeted, leading to financial loss and reputational damage. The indirect costs of such disruptions can be substantial, especially for small businesses that depend heavily on phone communication.
Measures for Prevention and Defense
In response to the rise of call bomber in attacks, various countermeasures have been developed. At the individual level, users can utilize call-blocking applications that detect and filter suspicious numbers or repetitive call attempts. Operating systems like Android and iOS offer built-in spam call protection features that can be configured for this purpose.
Telecommunication providers are also deploying advanced filtering technologies that monitor calling patterns and flag unusual activity. These systems can automatically block traffic from suspicious sources, particularly if it matches known patterns of abuse linked to call bomber in tools.
Enterprises have begun using cloud-based contact center platforms that include spam protection and call analytics. These systems monitor call frequency, duration, and geographic origin to detect irregularities. Additionally, companies can set up separate lines or virtual assistants to screen calls before routing them to actual staff.
Role of Developers and Online Platforms
Developers and hosting platforms also bear a degree of responsibility in the misuse of call bomber in tools. Open-source repositories often host scripts and frameworks that can be modified for malicious purposes. While many platforms have content guidelines against harmful code, enforcement remains a challenge due to the sheer volume of uploads.
Some developers include disclaimers stating that their tools are meant for educational purposes or penetration testing. However, the same tools can be repurposed by bad actors with little effort. Platforms such as GitHub, GitLab, or code-sharing forums must implement stricter moderation and work closely with cybersecurity experts to identify and remove harmful utilities.
Search engines and app stores have a role to play as well. Indexing or hosting links to call bomber in applications should be carefully regulated. By reducing the visibility and availability of such tools, the likelihood of misuse can be significantly curtailed.
Educating the Public and Promoting Responsible Use
One of the most effective ways to combat the misuse of call bomber in tools is through education. Awareness campaigns can inform users about the consequences of call bombing and the legal risks involved. Schools, colleges, and tech communities should emphasize the ethical use of digital tools and promote cybersecurity literacy.
Workshops and webinars conducted by law enforcement or ethical hacking groups can help demystify how such tools operate and why they must be handled responsibly. Encouraging white-hat hacking and responsible disclosure can redirect the technical talent behind these tools toward constructive purposes.
Promoting ethical standards in digital communication is essential. Just as society evolved norms around email, texting, and social media, similar frameworks must be developed around newer technologies like call bomber in tools. Community guidelines, peer education, and legal deterrents all contribute to creating a safe and respectful digital space.
Regulatory Oversight and International Cooperation
Given the cross-border nature of digital communication, regulating call bomber in tools requires international cooperation. Agencies such as Interpol and national cybercrime units must collaborate to track, investigate, and prosecute cases involving abuse of automated calling systems.
Legislation must evolve to address technological realities. Many current laws were drafted before the rise of internet telephony and cloud-based automation. Updating legal definitions, empowering enforcement bodies, and building public-private partnerships can strengthen the global response to call bombing and similar threats.
Telecom regulators can also issue guidelines to prevent the misuse of voice services. Licensing conditions, auditing mechanisms, and real-time monitoring systems can ensure that service providers do not inadvertently enable malicious activity.
Ethical Hacking and Security Testing
While call bomber in tools are often associated with abuse, they can also have legitimate uses in security testing. Ethical hackers and cybersecurity firms sometimes use controlled versions of such tools to assess the robustness of systems under simulated load conditions.
In such scenarios, explicit permission is obtained from the target, and strict safeguards are put in place to avoid disruption. These ethical applications help identify vulnerabilities in customer service lines, emergency numbers, or automated response systems, ultimately making them more secure.
Promoting responsible hacking and establishing legal frameworks for ethical security testing can reduce the stigma around automation tools and encourage constructive innovation.
Conclusion: A Tool That Demands Accountability
The story of the call bomber in today’s digital landscape is one of duality. On one hand, it is a technological tool with fascinating mechanics and automation capabilities. On the other, it has the potential to be deeply disruptive, invasive, and even dangerous when misused.
The challenge lies in understanding and regulating the use of such tools. Through legal oversight, technological innovation, community education, and ethical leadership, society can ensure that call bomber in applications are either safely utilized for legitimate purposes or removed from environments where they cause harm.
In an increasingly interconnected world, responsibility must be the guiding principle behind all technological advancement. The existence of tools like the call bomber in is not inherently negative—what truly matters is how we choose to use them.
You may like
Trending

 Blog8 months ago
Blog8 months ago[PPT] Human Reproduction Class 12 Notes
- Blog8 months ago
Contribution of Indian Phycologists (4 Famous Algologist)
- Blog8 months ago
PG TRB Botany Study Material PDF Free Download

 Blog8 months ago
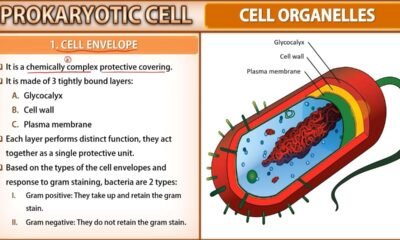
Blog8 months agoCell The Unit of Life Complete Notes | Class 11 & NEET Free Notes

 Blog8 months ago
Blog8 months ago[PPT] The living world Class 11 Notes

 Blog8 months ago
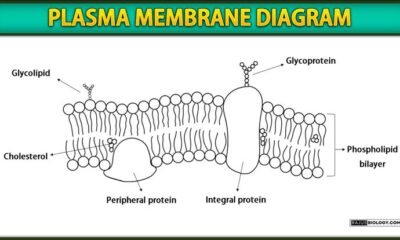
Blog8 months agoPlasma Membrane Structure and Functions | Free Biology Notes

 Blog8 months ago
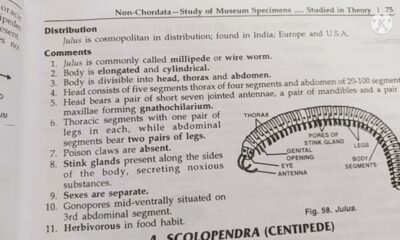
Blog8 months agoJulus General Characteristics | Free Biology Notes

 Blog8 months ago
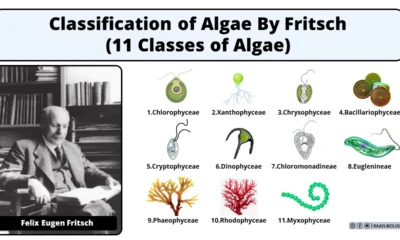
Blog8 months agoClassification of Algae By Fritsch (11 Classes of Algae)