Blog
Cybersecurity Mistakes a Pen Testing Service Can Help You Avoid

You might have read tons of content on avoiding pitfalls while running a penetration testing across the IT environment. In this blog, we take a different perspective.
In an age where data breach headlines arrive with the same regularity as quarterly reports, IT leaders should treat security like a practice worth rehearsing and repeating. For executives like CISOs, CTOs, CEOs and founders, the right way forward is not just buying tools; it is learning where your defences silently fail. A Pen Testing Service does more than find bugs. It exposes false confidence and helps translate technical findings into boardroom decisions.
What do We Mean?
Why traditional checks fail? That’s because organisations often rely on point-in-time scans or compliance reports and assume the job is done. They forget that networks, apps and teams evolve and modernize daily. Security that may seem to be alright on a given Monday could turn as a risk by Friday for the firm.
Also, scanning alone rarely shows whether your team can detect and respond when an adversary is inside. This is where a Pen Testing Service adds context. It simulates realistic attacks, tests detection and exposes the human and process gaps that automated tools miss.
Five Common Mistakes and How Pen Testing Fixes Them
Even the most security-mature businesses slip up in predictable ways. A Pen Testing Service shines a light on these blind spots and offers clear, actionable fixes before attackers can exploit them.
- Vulnerability Counts as Risk
Many teams equate a low vulnerability number with safety. But numbers hide nuance.
A single exploitable misconfiguration on an internet-facing server can be far more dangerous than dozens of low-severity findings. A Pen Testing Service prioritises exploitability and business impact, showing which holes will actually let an attacker in and which are just noise. - Treating Assets as Static
Cloud workloads, CI/CD pipelines and third-party integrations change constantly. Static inventories lead to blind spots. Pen testers probe the dynamic parts of your environment and find the forgotten assets attackers love. In short, pen testing reveals the status of your attack surface. - Human & Process Weaknesses
Cybersecurity is the sum of technology and human functions. Social engineering, poor change controls and unclear incident playbooks are often the real threat vectors. Such engagements can include phishing simulations and workflow tests that measure human risk and readiness, turning abstract process gaps into concrete, fixable findings. - Relying on Snapshots
Annual or bi-annual reviews are out of step with modern development cycles. Snapshot testing misses regressions introduced between assessments. Continuous engagement through periodic retests or integration into CI pipelines keeps security aligned with rapid releases. Plus, it reduces the chance of a regression becoming an incident. - Not Practising Detection, Response
Discovering a vulnerability is one thing; detecting and containing an active exploit is another. Red vs. blue exercises are not theatre but rehearsals. A mature Pen Testing Service validates whether your monitoring, alerting and response work under pressure. And it helps sharpen the coordination between security, dev and ops teams when times matter.
A Different Angle: Pen Testing as a Rehearsal
Most content about penetration testing focuses on technical findings. The more strategic view is to treat security as a rehearsal for real incidents. A Pen Testing Service is a dry run for your playbook: it reveals weaknesses in communication, authority, escalation and decision-making. Leaders who think like directors—running scenarios, clarifying roles, and measuring response times—see pen testing pay off far beyond patched CVEs.
Pen Testing: How to Measure the Value
ROI for security work is often solved backward: after an incident. Instead, measure improvements in mean time to detect (MTTD), mean time to respond (MTTR), reduction in exploitable findings and the percentage of high-impact issues remediated within defined SLAs. A Pen Testing Service should deliver these metrics alongside clear remediation roadmaps, so executives can judge progress in business terms, not just technical jargon.
Choosing a Pen Testing Partner that Changes Behaviour
The right partner explains risk in business language, helps prioritize remediation and trains your teams to change behaviour. Look for services that combine technical depth with advisory capability. Someone who can run an exploit, then sit with your engineering teams and explain how to prevent it next time. A Pen Testing Service that leaves a stronger process and a better-trained team has delivered lasting value.
Leaders should start by defining critical assets—customer data, payment flows, admin consoles, and insist the test emulate real adversaries targeting those assets. Require both technical exploitation and tabletop rehearsals for decision-makers. Ask vendors to include remediation support and a retest clause so fixes are validated.
Demand business-friendly metrics: MTTD, MTTR, percentage of high-impact issues closed. Finally, formalise an annual adversary-emulation exercise and integrate findings into sprint planning regularly.
Common Pushbacks and How You can Respond
“We don’t have the budget.” This is a common pushback. Security leaders can frame pen testing as risk reduction tied to business outcomes. Slower detection or a public breach cost far more in revenue and trust than proactive testing.
“We’re compliant, so we’re safe.” This is another thing which stakeholders often speak about. But compliance is just a foundation and not a guarantee. This kind of testing moves the conversation from paperwork to proof.
“We’ll handle it in-house.” Well, in-house teams often lack the adversary mindset. An external testing partner brings fresh perspectives and attack craft that internal reviews miss.
How CyberNX’s Pen Testing Service Can Help Your Business
At CyberNX, the team of seasoned experts are armed with must-have certifications like OSCP, CEH, and CISSP, and uses cutting-edge tools and the latest adversary TTPs to identify high-risk components in record time.
The pentesters map out exactly how to:
- Find vulnerabilities before attackers do
- Close compliance gaps
- Gauge your security team’s response speed
- Assess the real business impact of an attack
- Implement targeted remediation.
Every test mirror real-world threat actor behaviour, from reconnaissance to exploitation and post-exploitation, so findings aren’t theoretical, they’re battle-tested.
As a CERT-IN empanelled provider, they meet India’s highest cybersecurity standards, making us trusted by BFSI, fintech, SaaS and healthcare sectors. Our detailed reports go beyond technical details, delivering a strategic roadmap aligned with your risk appetite, compliance mandates and business goals, transforming insights into lasting resilience.
Conclusion
Security that survives an audit but fails a simulated attack is a common, costly mismatch. Moving from checkbox compliance to continuous rehearsal requires both discipline and the right partner.
Choose CyberNX as a trusted, reliable and proven penetration testing partner. Their Pen Testing Service does more than point out flaws. It rewires how organizations think about risk, response and resilience. For leaders responsible for everything from uptime to reputation, CyberNX experts help you discover your weak link in a controlled exercise and helps improve your security posture.
FAQs
How often should a business invest in a Pen Testing Service?
For fast-moving industries like fintech or SaaS, testing every 3–6 months is ideal. For others, at least once a year—plus after any major infrastructure or application change—is critical to stay ahead of emerging threats.
Can a Pen Testing Service help with board-level cybersecurity reporting?
Yes. Modern penetration tests can deliver executive-ready summaries that translate technical findings into business impact, risk ratings, and ROI metrics, making them easy for boards and leadership teams to act on.
Does a Pen Testing Service simulate insider threats?
Absolutely. Some engagements are tailored to mimic malicious insiders—testing privilege escalation, access abuse, and detection gaps that outsiders wouldn’t exploit as easily.
How is a Pen Testing Service different from a vulnerability scan?
A scan lists weaknesses; a Pen Testing Service actively exploits them in a safe, controlled manner to show the real-world impact and likelihood, providing a far more accurate risk picture.

 Blog8 months ago
Blog8 months ago[PPT] Human Reproduction Class 12 Notes
- Blog8 months ago
Contribution of Indian Phycologists (4 Famous Algologist)
- Blog8 months ago
PG TRB Botany Study Material PDF Free Download

 Blog8 months ago
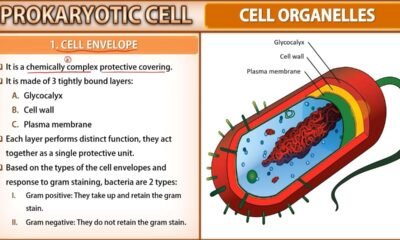
Blog8 months agoCell The Unit of Life Complete Notes | Class 11 & NEET Free Notes

 Blog8 months ago
Blog8 months ago[PPT] The living world Class 11 Notes

 Blog8 months ago
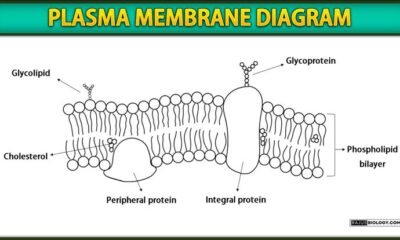
Blog8 months agoPlasma Membrane Structure and Functions | Free Biology Notes

 Blog8 months ago
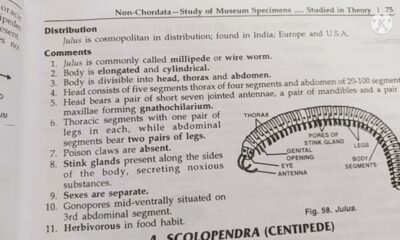
Blog8 months agoJulus General Characteristics | Free Biology Notes

 Blog8 months ago
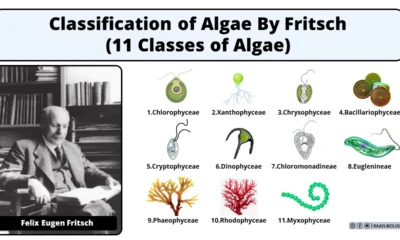
Blog8 months agoClassification of Algae By Fritsch (11 Classes of Algae)